TREZOR
Trezor Login — What “Logging In” Really Means for Your Hardware Wallet
A friendly, deep-dive guide for beginners and intermediate users explaining how to access your Trezor, sign transactions, and stay safe — without confusing "accounts" with custody.
Audience
Beginner → Mid-level
Short answer: there is no centralized "Trezor account" to log into — instead you connect your physical device to software (Trezor Suite, browser extensions, or Web3 wallets) and authenticate by physically approving actions on the device. This guide explains each path, the security model behind it, and practical steps for a safe and smooth Trezor login experience.
We’ll cover: connecting via USB/WebUSB, Trezor Bridge vs. Suite, integrating with MetaMask or Web3 DApps, passphrases, recovery seed hygiene, and troubleshooting. Expect analogies, checklists, and a handy comparison grid to help you choose the right flow.
What “Trezor Login” actually is
Unlike email or exchange logins, Trezor’s model is physical and cryptographic: you unlock the device with a PIN (local), optionally add a passphrase (extra hidden layer), and then confirm transactions by pressing buttons or touching the screen on the hardware. Software like Trezor Suite, the web bridge, or integrations like MetaMask only act as a user interface and never hold your private key.
Core components:
- Private Key — never leaves the device.
- PIN — local unlock control.
- Seed phrase — offline backup to recover funds.
- Passphrase — optional, creates hidden wallets.
Quick glossary (terms you'll see)
Private key — cryptographic secret proving ownership.
Seed phrase — 12–24 words that back up your keys.
Passphrase — optional extra word for hidden wallets.
2FA — two-factor authentication; unrelated to Trezor’s local PIN but often used with exchanges.
Self-custody — you control the keys.
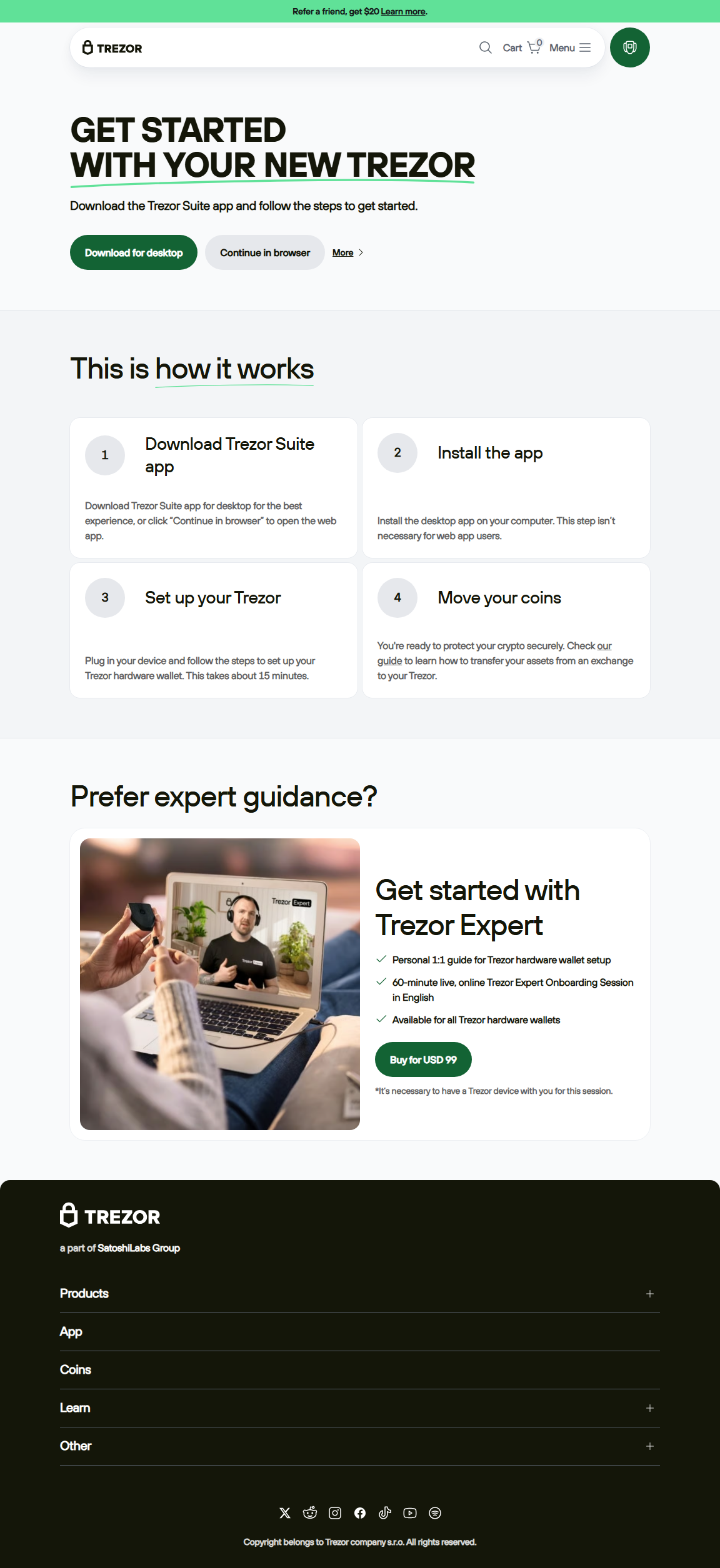
Flow A — Trezor Suite (Desktop)
Best for: portfolio management, firmware updates, straightforward send/receive.
- Download and install Trezor Suite from trezor.io (type URL manually).
- Connect device via USB, enter PIN to unlock.
- Confirm device prompts to initialize or restore using seed phrase.
- Manage accounts and sign transactions by approving on-device.
Flow B — Web + Trezor Bridge / WebUSB
Best for: quick checks, browser-based apps (when Suite not needed).
- Install Trezor Bridge (or use WebUSB-supported browsers).
- Open the web app (e.g., wallet interface), connect device.
- Unlock with PIN, confirm actions on device's screen.
- Be cautious: always verify web app domain and on-device address strings.
Flow C — MetaMask & Web3 DApps
Best for: DeFi interactions while keeping keys offline.
- Install MetaMask browser extension and choose "Connect Hardware Wallet".
- Select Trezor, connect via Bridge/WebUSB and pick accounts to expose (public keys only).
- When initiating a swap or contract call, sign on the Trezor device after verifying the data shown.
- Tip: For complex contracts, verify calldata and amounts on-device where possible.
Security spotlight
Think of the Trezor device as a locked signing machine. The computer asks for signatures (the "what"), but the device holds the stamp (the private key) and physically stamps the transaction only when you approve. That physical confirmation is the key defense against remote attacks and malware.
Login & Access Comparison
Trezor Suite
Desktop app; direct firmware updates; recommended for daily management. PIN required. Highest UX for firmware handling.
Web + Bridge/WebUSB
Fast browser flows; useful for lightweight checks. Bridge is required for some browsers; check for phishing clones before connecting.
MetaMask / DApps
MetaMask exposes public addresses; signing still happens on-device. Best for DeFi, but verify contract details on the Trezor itself.
Troubleshooting — common login hiccups
Device not detected: Try a different USB cable/port, enable WebUSB in browser flags, or install Trezor Bridge.
Forgot PIN: Entering the wrong PIN repeatedly will factory-reset the device — you can restore with your seed phrase. Keep the seed safe.
Browser shows "untrusted site": Double-check the URL manually. Phishing pages often mimic Trezor UI.
Transaction stuck: Cancel or reset nonce in your sending app (if supported), then reinitiate with correct gas/fee settings and sign on-device.
Quick recovery checklist
- Locate your seed phrase (paper/metal backup).
- Get a new Trezor or compatible recovery device.
- Use "Recover wallet" during setup and enter words exactly.
- Set a fresh PIN and consider adding a passphrase if you previously used one.
Top mistakes users make thinking about "logging in"
- Expecting a central account: Trezor does not create a cloud account. Your keys and identity live with you.
- Using email/password metaphors: Your security is based on seed phrase + PIN/passphrase, not passwords you can reset by email.
- Entering seed online during "login": Never input recovery words into websites or apps — only on-device during recovery.
- Assuming exchanges equal custody: Logging into an exchange is not the same as unlocking your hardware wallet — custody differs dramatically.
FAQ — short answers
Q: Do I need an account to use Trezor?
A: No centralized account — you use the device and your seed phrase.
A: No centralized account — you use the device and your seed phrase.
Q: Is my seed a kind of login?
A: The seed is the ultimate backup of your private keys; treat it like an irreplaceable master key, not a password.
A: The seed is the ultimate backup of your private keys; treat it like an irreplaceable master key, not a password.
Q: Can I use Trezor with multiple computers?
A: Yes — as long as those computers have Trezor Suite or Bridge/WebUSB installed and you physically connect & unlock the device.
A: Yes — as long as those computers have Trezor Suite or Bridge/WebUSB installed and you physically connect & unlock the device.
Q: Is the passphrase required?
A: No — it’s optional and provides hidden wallets. Use it only if you understand its permanence and storage needs.
A: No — it’s optional and provides hidden wallets. Use it only if you understand its permanence and storage needs.
FAQ — security-focused
Q: Can someone reset my Trezor remotely?
A: No. Physical possession and PIN/passphrase are required. Remote attacks can’t extract keys from a properly used device.
A: No. Physical possession and PIN/passphrase are required. Remote attacks can’t extract keys from a properly used device.
Q: If my computer is hacked, can they steal from my Trezor?
A: Not without your PIN and physical confirmation on the device. Still, avoid approving transactions you don’t understand.
A: Not without your PIN and physical confirmation on the device. Still, avoid approving transactions you don’t understand.
“Logging in with a hardware wallet is not about a username — it’s about proving ownership with a physical key.”
— Practical security principle for self-custody
Final checklist before your next Trezor login
- Type the official URL (or open Trezor Suite); never click suspicious links.
- Connect the device, enter your PIN, and verify on-device prompts — that’s your true authentication step.
- For DeFi or contract interactions, read calldata and confirm values on the device screen.
- Keep your seed phrase offline (paper or metal) and consider multisig for very large holdings.
- Remember the core terms: private key, seed phrase, passphrase, self-custody, 2FA.
Conclusion — own the process, not the password
“Trezor Login” is a useful shorthand, but what you’re really doing is connecting a trusted piece of hardware and authorizing actions with physical confirmation. This model moves security from brittle passwords and centralized logins into a place you control: your device and your seed. Practice good seed hygiene, prefer official software (Trezor Suite / Bridge), verify everything on-device, and you’ll have a resilient, understandable login flow that scales from casual holdings to serious DeFi and NFT activity.
Start each session by typing the official address or opening the official Suite, connect your Trezor, and authenticate safely — that’s the essence of a secure Trezor Login.